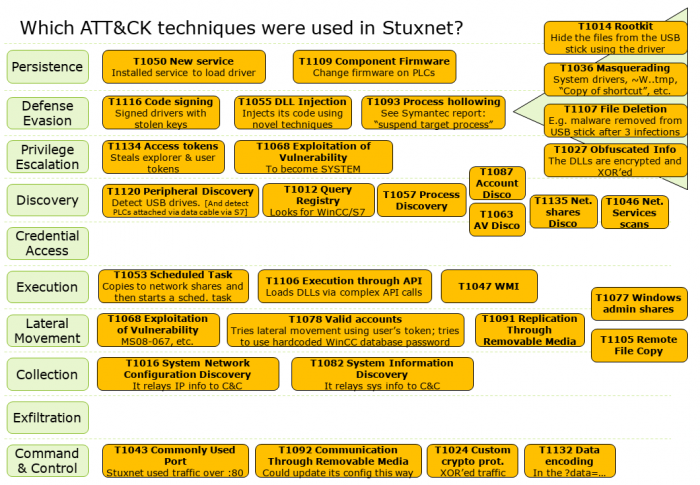
Mapping Stuxnet on the ATT&CK framework
The MITRE ATT&CK framework is a great tool for blue teams.
As an exercise, I tried mapping the Stuxnet attack onto the ATT&CK framework. As a source, I used the excellent Symantec Stuxnet paper.
- I tried cramming it all into one slide, sorry for that. Defense evasion is indeed that big.
- There are multiple ways to do the mapping. There could also be mistakes (caveat emptor). I welcome any bugfixes.
- The credential access row is empty, since from what I read it used the user’s credential token not their actual passwords. The exfiltration row is empty because the paper shows that this instance was primarily meant for infecting the SCADA systems. Of course, the malware was able (via its C&C connection) to have exfiltration modules, but these were not discussed.
PDF version: ATT&CK – Stuxnet.